SOC Intelligence That Doesn't Sleep.
PhantomX is an autonomous SOC platform built to accelerate detection, investigation, and response — without adding analyst headcount. Continuous coverage. Machine-speed execution. Human-quality judgment.
An Autonomous SOC Platform Built for the Realities of Modern Security Operations
PhantomX by Vigilix is purpose-built for security teams dealing with high alert volumes, analyst capacity constraints, and the demand for faster response. Rather than adding another monitoring tool, PhantomX acts as an operational layer that handles the detection-to-response cycle autonomously — surfacing what matters, enriching each incident automatically, and executing response actions based on pre-configured playbooks.
The result is a SOC that operates faster with less analyst burnout and more consistent outcomes — whether staffed by your internal team, co-managed with Vigilix, or fully operated by Vigilix experts.
See PhantomX at Work
A real-time look at the PhantomX console — from the NIST-aligned Mission Control dashboard to the autonomous multi-agent execution engine.
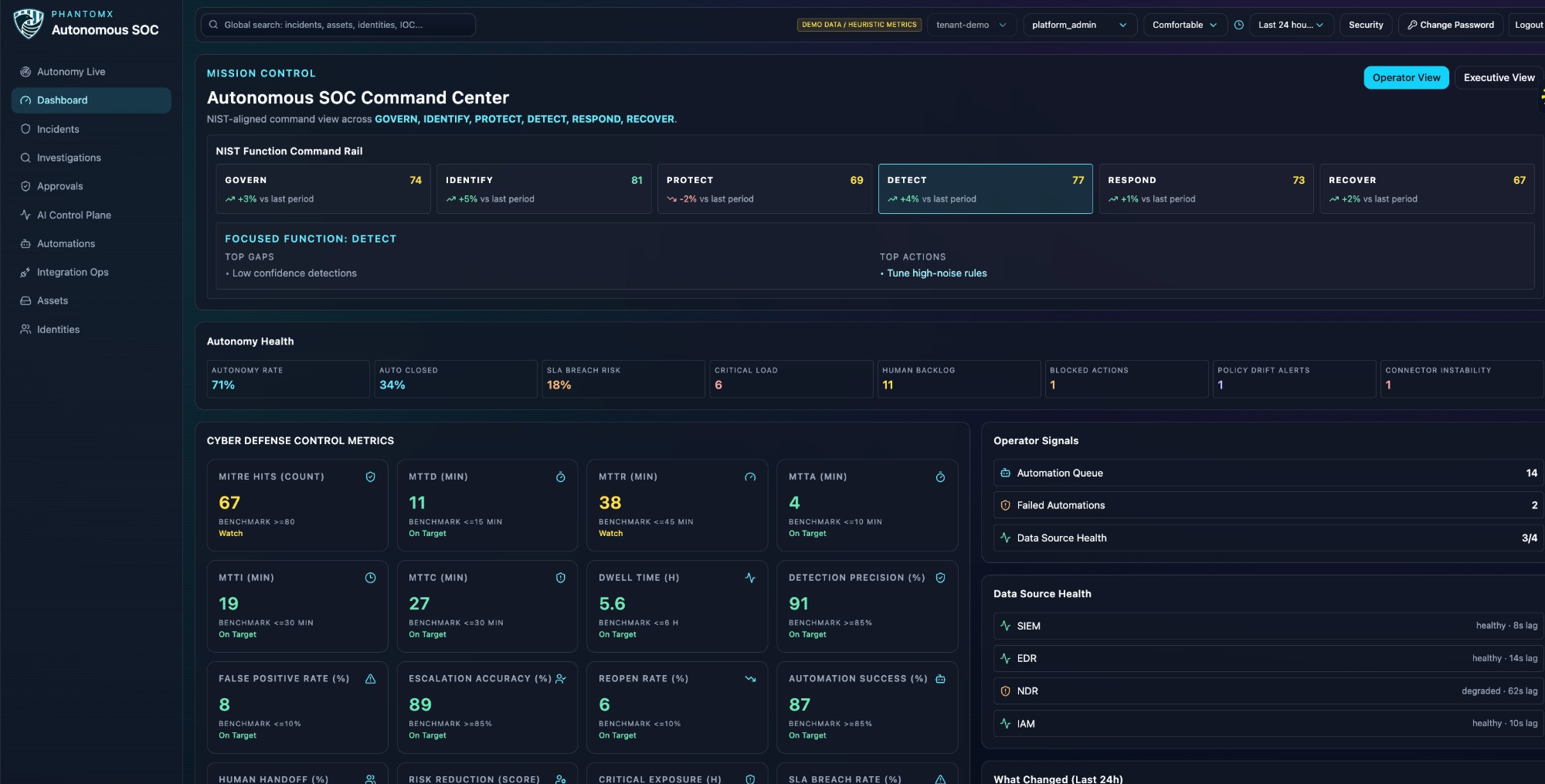
Autonomous SOC Command Center
A unified, NIST CSF–aligned dashboard giving SOC operators real-time visibility across all six functions — Govern, Identify, Protect, Detect, Respond, and Recover — with live scores, autonomy health metrics, and cyber defense control benchmarks.
- NIST Function Command Rail with live scoring
- Autonomy Rate, SLA Breach Risk & Critical Load
- MTTD, MTTR, MTTA benchmarks vs targets
- Operator signals & data source health
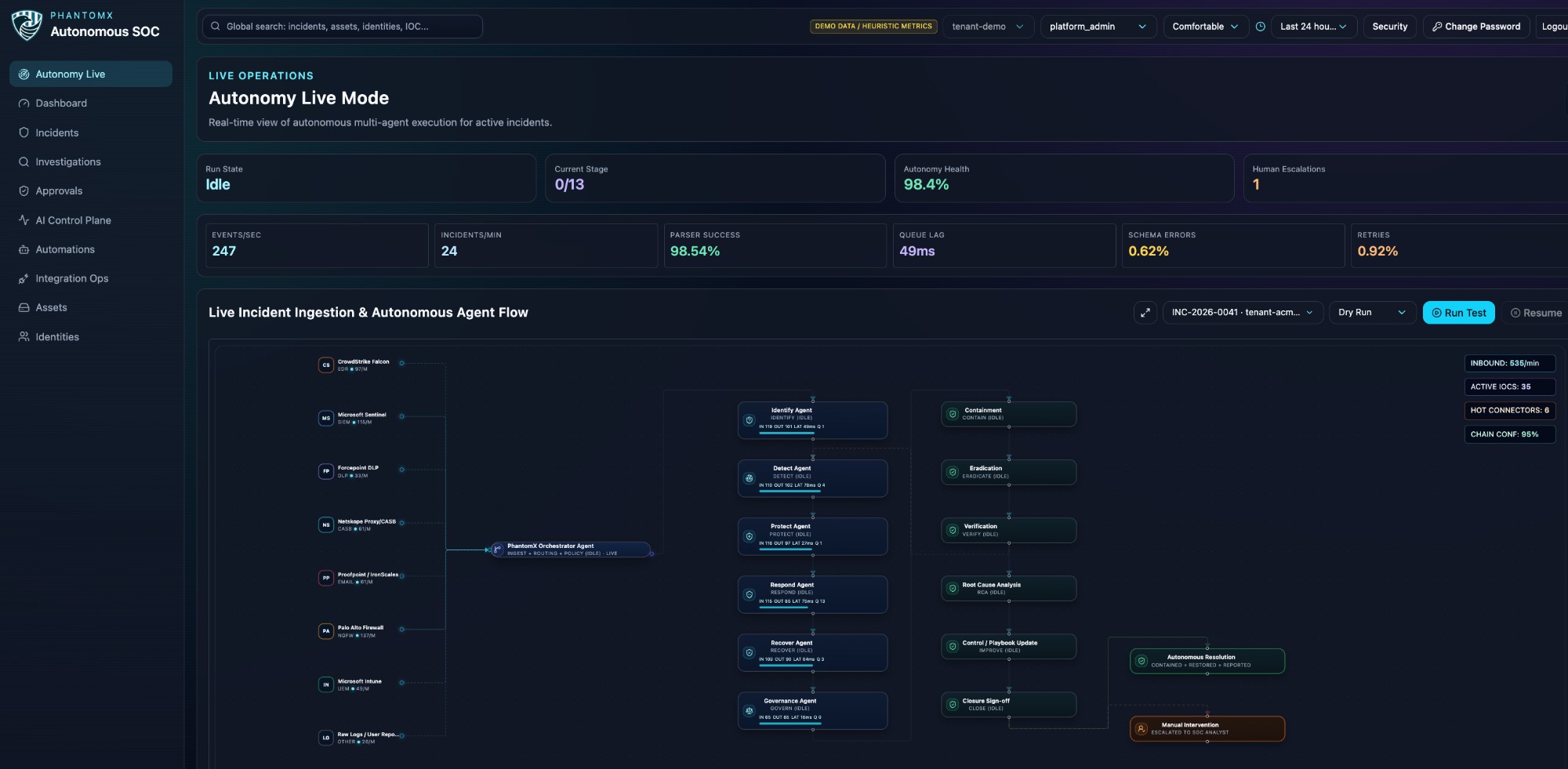
Multi-Agent Execution in Real Time
Autonomy Live Mode surfaces the full PhantomX agent pipeline as it executes — ingesting events, orchestrating agents across the NIST lifecycle, and driving incidents to autonomous resolution with no human intervention required for routine threats.
- 247 events/sec processed in real time
- PhantomX Orchestrator routing across 13 agents
- 98.4% autonomy health, 49ms queue lag
- Full visual pipeline from ingest to resolution
Six Pillars of Autonomous SOC Operations
PhantomX delivers a complete, integrated set of capabilities that cover every stage of the security operations lifecycle.
Autonomous Detection
PhantomX monitors endpoint, network, cloud, and identity telemetry continuously, applying behavioral analytics to surface high-confidence threats without requiring manual triage of every alert.
Intelligent Correlation
Disparate events from across your environment are correlated into unified incidents, mapped to MITRE ATT&CK techniques, and scored by severity — so analysts see context, not raw alerts.
Investigation Enrichment
Every incident is automatically enriched with threat intelligence lookups, asset context, user history, and timeline reconstruction — giving analysts a complete picture before they touch a keyboard.
Response Orchestration
Pre-built and customizable response playbooks execute containment, isolation, and remediation actions across integrated tools — from endpoint agents to cloud APIs — in seconds, not minutes.
SOC Workflow Automation
Ticket creation, analyst assignment, escalation paths, and cross-tool coordination are fully automated based on configurable logic — eliminating friction from manual SOC workflow management.
Operational Visibility
A unified SOC console provides real-time visibility into incident queues, detection coverage, automation performance, analyst activity, and mean-time-to-respond trends — all in one place.
From Signal to Resolution — Automatically
PhantomX operates a continuous, closed-loop security workflow that takes your environment from raw telemetry to resolved incidents with minimal analyst intervention required.
Connect Your Environment
PhantomX integrates with your existing SIEM, EDR, cloud logs, identity providers, and network tools via pre-built connectors. Setup is structured and guided for fast time-to-value.
Ingest & Normalize
Telemetry is ingested, normalized, and enriched with asset context and threat intelligence before hitting the detection engine — ensuring high-quality signal from the start.
Detect & Correlate
Behavioral detection rules and ML models identify suspicious patterns. PhantomX clusters related events into correlated incidents with full kill-chain context.
Investigate Automatically
Each incident triggers an automated investigation workflow — pulling in asset data, running IOC lookups, reconstructing timelines, and documenting findings in structured case notes.
Respond & Contain
Response playbooks execute appropriate containment and remediation actions. High-confidence actions run automatically; ambiguous situations are escalated to analysts with full context pre-loaded.
Measure & Improve
The operational dashboard tracks detection coverage, automation rates, analyst performance, and response timing — surfacing gaps and driving continuous improvement of your security program.
Where PhantomX Delivers Impact
PhantomX is designed to handle the highest-volume, highest-friction scenarios in modern security operations.
Alert Triage Automation
PhantomX automatically classifies and prioritizes incoming alerts based on severity, context, and historical patterns — reducing analyst triage time by over 80% without sacrificing coverage.
Endpoint Incident Response
When an endpoint shows signs of compromise, PhantomX gathers process trees, network connections, and file activity, then executes isolation playbooks while notifying the response team.
Suspicious Cloud Activity Analysis
Anomalous API calls, privilege escalations, and unusual resource access patterns trigger automated investigation workflows correlating cloud events with identity and access context.
Threat Escalation Workflows
Incidents meeting defined criteria are automatically escalated to the right analyst with full incident context, reducing decision latency and ensuring the right skills are applied to the right threats.
Analyst Workload Reduction
By automating the detection-investigation-response cycle for common incident types, PhantomX directly reduces analyst toil — enabling security teams to operate at higher strategic levels.
Flexible Deployment to Match Your Team
PhantomX adapts to your current security maturity and capacity — from self-managed deployments to fully operated services.
Platform Only
Deploy PhantomX in your environment and configure it to your team's workflow. Ideal for security teams with existing analyst capacity who want autonomous detection and automation capability.
- Full platform access
- Pre-built connectors & playbooks
- Self-serve onboarding support
- Documentation & training resources
Co-Managed
Your team retains ownership of investigations and decisions, while Vigilix experts assist with platform tuning, playbook development, detection engineering, and escalation support.
- All Platform Only features
- Vigilix analyst augmentation
- Detection engineering support
- Monthly program reviews & reporting
Managed by Vigilix
Vigilix operates PhantomX on your behalf — 24/7 monitoring, triage, investigation, and response handled by our expert SOC team, with full transparency into every action taken.
- All Co-Managed features
- 24/7 Vigilix SOC coverage
- Dedicated security team
- SLA-backed response times
Connects to Your Existing Stack
PhantomX is designed to work with the security tools you already have — not replace them. Pre-built connectors span the major categories of the enterprise security stack.
SIEM & Log Management
Splunk, Microsoft Sentinel, Elastic, IBM QRadar
Endpoint Detection & Response
CrowdStrike, SentinelOne, Microsoft Defender, Carbon Black
Cloud Platforms
AWS CloudTrail, Azure Sentinel, GCP SCC, Kubernetes audit logs
SOAR & Ticketing
Splunk SOAR, ServiceNow, Jira, PagerDuty
Identity & Access
Okta, Azure AD, CyberArk, Duo
Threat Intelligence
MISP, VirusTotal, Recorded Future, AlienVault OTX
Don't see your tool? Contact us about custom integrations.
See PhantomX in Action.
Request a personalized demo and discover how PhantomX reduces detection time and analyst burden in environments like yours.